While there’s been no end to the discussion of the benefits the Internet of Things will bring to our daily lives, it seems some of the more concerning byproducts –referred to as “unintended consequences” – have been, for the most part, downplayed. Concerns like who owns the data generated by consumer or medical wearable devices? What about data generated by devices in cars? For instance, when you rent a car and use the Bluetooth capabilities to connect your phone and download the phone book, what happens to that information when you return the vehicle? Or how about those devices insurance companies issue to track driving habits so you can get lower rates? Is that theirs to sell or yours? And while autonomous cars may reduce the number of fatalities from car accidents, an unintended consequence of this will be a reduction in organs available for transplants. These issues and more made for interesting presentations and great conversation at the recent SEMI Arizona Breakfast Forum, October 17, 2015, at Freescale Semiconductor.
The topic of the morning was “Monetizing the IoT: Opportunities and Challenges for the Semiconductor Industry,” and featured speakers from SEMICO Research, Freescale Semiconductor, Intel, PADT, Medtronic, and Arizona State University. Making the IoT secure and protecting user data has been an ongoing concern. Not surprisingly, it turns out these issues are intimately linked with monetizing the IoT.
What Monetizing the IoT means for Semiconductors
In his presentation, Tony Massimini, SEMICO Research noted that clearly, the value of the IoT is the data, but up until now the focus has been on services using sensor data. The question is, how is the semiconductor industry going to monetize IoT for our benefit? “We are providing underpinnings,” noted Massimini. “Without the semiconductor industry, there is no IoT.” Because semiconductor and MEMS devices are being commoditized, we need to find ways to add value to the silicon.
Massimini explained that one way to counter asking selling price (ASP) decline for ICs is to add features like higher performance cores, large memory, more peripherals, wireless, security, and low power. Sensor fusion algorithms also add value to the silicon. Additionally, broadening portfolios through mergers and acquisitions of sensor fusion companies allows for companies to offer system solutions, which are also added value. In his conclusion, he emphasized that on top of all of this, security is a key factor for IoT growth.
How Security is Linked to IoT Adoption
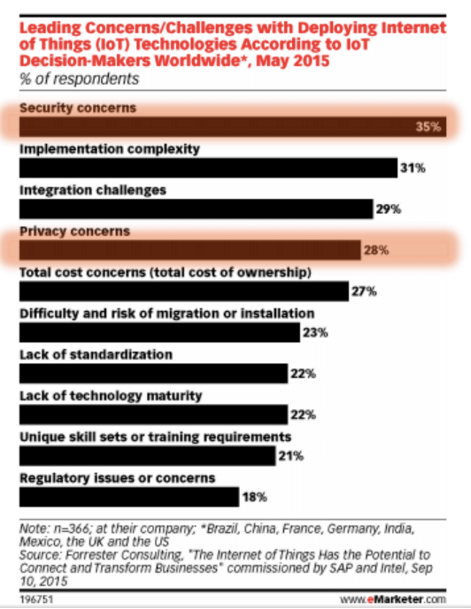
Intel’s David Formisano echoed that sentiment, noting that security and privacy concerns are high up on the list of challenges to IoT adoption (Figure 1). He pointed out that security for the IoT differs from embedded systems because embedded systems aren’t connected. Ian Chen, Freescale, added that security for sensors is different than cyber security “We’re not talking about just losing consumer information and identity theft. Lack of IoT security is about blowing things up,” he said.
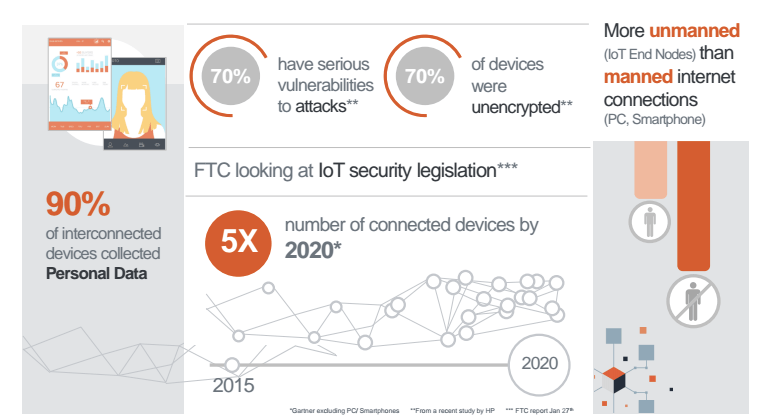
According to an FTC report on IoT Security regulation, while 90% of interconnect devices collect personal data, 70% of those are unencrypted and are vulnerable to attacks, noted Chen (Figure 2).
Formisano shared a quote from the National Security Telecommunications Advisory Committee (NSTAC) Report to the President on the Cybersecurity Implications of the Internet of Things, which stated: “There is a small—and rapidly closing—window to ensure that IoT is adopted in a way that maximizes security and minimizes risk.”
Trusted data is the essential ingredient to securing the IoT, explained Formisano. The recipe begins with hardening devices to secure communications, and analyze and monitor the data while managing the complexity. This is something Intel has been working on for some time, and has already implemented Enhanced Privacy Identification (EPID), which is a unique hardware-based privacy ID. In simple terms, this creates encrypted anonymous data that, for example, allows a utility company to know the customer lives in a particular town and know everything that’s going on in the house without knowing who that person is. EPID is signed with a public key at the group level and ensures devices are talking to the correct group.
An industrial application for the EPID key is device provisioning. Let’s say tools have smart devices embedded to track the users productivity. EPID keys can prevent use of a tool by anyone other than its assignee. EPID is ISO Standard for Authentication/TCS Standard for Attestation, because the IoT is bigger than one company, and the reality is that we need lots of components made by different companies. Atmel and Microchip are implementing EPID. The ecosystem is expanding, said Formisano, and EPID in the Cloud can create a secure pipeline of encrypted, anonymous data, and protect secure transactions. Formisano said 1.1 billion EPID credentials are already deployed worldwide, and it can easily be scaled for the IoT.
While this is great news for new devices, what about the ones already out there, gathering data, that aren’t secure? Or what about a device for which hardened security goes out of warranty? Formisano says there are ways to secure existing devices, although it’s more challenging.
Consumer Culture for IoT Adoption
Even with companies addressing security and privacy issues using hardware and software solutions, full adoption may require a paradigm shift and a new way of thinking about our data, noted the experts. Many of the questions posed in the opening paragraph of this blog can’t really be addressed by devices, but are more about the shift in consumer thinking. The younger generation is willing to give up certain rights to data for the convenience afforded them by the IoT capturing that data. But they still need to be concerned about the impact it will have.
While security and privacy are two different challenges to IoT adoption, both involve data. As previously stated, data is also where the value lies when it comes to monetizing the IoT. Bottom line: Data is the heart of IoT. We must protect it and protect our privacy simultaneously. This needs to quickly move to the top of the “things to do” list, before the window of opportunity closes. ~ FvT